Optimizing Group Management and Cryptographic Techniques for Secure and Efficient MTC Communication
Main Article Content
Abstract
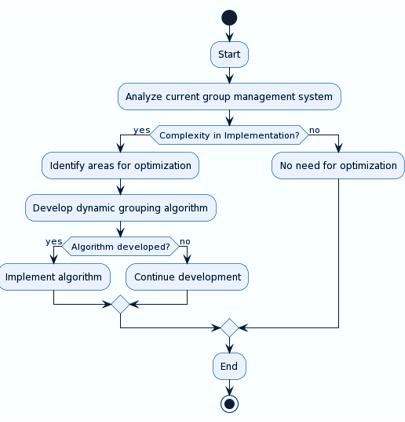
This paper proposes a novel, multifaceted approach to enhance security and efficiency in Machine-Type Communication (MTC) that addresses limitations of the Adaptive Hierarchical Group-based Mutual Authentication and Key Agreement (AHGMAKA) protocol. AHGMAKA, designed for securing hierarchical groups of resource-constrained devices in MTC networks, can suffer from high overhead. Our approach integrates advancements in cryptographic techniques (optimized AMAC and lightweight encryption), optimization algorithms (dynamic grouping and lightweight group management protocol), and adaptive network management strategies. Exclamation The optimized AMAC reduces key length and leverages hardware acceleration, while lightweight encryption methods prioritize efficiency. Performance analysis demonstrates significant improvements: execution time reduced by 58.33%-63.79% and energy consumption reduced by 58.33%-64.41%. exclamation However, limitations like the security-efficiency trade-off and legacy device constraints are acknowledged. Future work explores machine learning-based group management, post-quantum cryptography adoption, hardware-assisted acceleration, and standardization efforts. Exclamation This research paves the way for secure and efficient MTC communication in the evolving Internet of Things landscape.
Article Details

This work is licensed under a Creative Commons Attribution-NonCommercial 4.0 International License.
IJCERT Policy:
The published work presented in this paper is licensed under the Creative Commons Attribution 4.0 International (CC BY 4.0) license. This means that the content of this paper can be shared, copied, and redistributed in any medium or format, as long as the original author is properly attributed. Additionally, any derivative works based on this paper must also be licensed under the same terms. This licensing agreement allows for broad dissemination and use of the work while maintaining the author's rights and recognition.
By submitting this paper to IJCERT, the author(s) agree to these licensing terms and confirm that the work is original and does not infringe on any third-party copyright or intellectual property rights.
References
Krishna Jyothi, K., & Chaudhari, S. (2022). A secure cluster-based authentication and key management protocol for machine-type communication in the LTE network. International Journal of Computers and Applications, 44(12), 1150-1160.
Singh, G., & Shrimankar, D. D. (2018). Dynamic group based efficient access authentication and key agreement protocol for MTC in LTE-A networks. Wireless Personal Communications, 101, 829-856.
Choi, D., Choi, H. K., & Lee, S. Y. (2015). A group-based security protocol for machine-type communications in LTE-advanced. Wireless networks, 21, 405-419.
Lai, C., Lu, R., Zheng, D., Li, H., & Shen, X. (2015). Toward secure large-scale machine-to-machine comm unications in 3GPP networks: chall enges and solutions. IEEE Communications Magazine, 53(12), 12-19.
Roychoudhury, P., Roychoudhury, B., & Saikia, D. K. (2018). Provably secure group authentication and key agreement for machine type communication using Chebyshev’s polynomial. Computer Communications, 127, 146-157.
Jyothi, K. K., & Chaudhari, S. (2020). Cluster-based authentication for machine type communication in LTE network using elliptic curve cryptography. International Journal of Cloud Computing, 9(2-3), 258-284.
Basudan, S. (2020). LEGA: a lightweight and efficient group authentication protocol for massive machine type communication in 5G networks. Journal of Communications and Information Networks, 5(4), 457-466.
Lai, C., Li, H., Lu, R., Jiang, R., & Shen, X. (2014, June). SEGR: A secure and efficient group roaming scheme for machine to machine communications between 3GPP and WiMAX networks. In 2014 IEEE International Conference on Communications (ICC) (pp. 1011-1016). IEEE.
Lai, C., Lu, R., Zheng, D., Li, H., & Shen, X. S. (2016). GLARM: Group-based lightweight authentication scheme for resource-constrained machine to machine communications. Computer Networks, 99, 66-81.
Lai, C., Li, H., Li, X., & Cao, J. (2015). A novel group access authentication and key agreement protocol for machine‐type communication. Transactions on emerging telecommunications technologies, 26(3), 414-431.
Parne, B. L., Gupta, S., & Chaudhari, N. S. (2018). Segb: Security enhanced group based aka protocol for m2m communication in an iot enabled lte/lte-a network. IEEE Access, 6, 3668-3684.
Mahmood, N. H., Böcker, S., Munari, A., Clazzer, F., Moerman, I., Mikhaylov, K., ... & Seppänen, P. (2020). White paper on critical and massive machine type communication towards 6G. arXiv preprint arXiv:2004.14146.
Jyothi, K. K., & Chaudhari, S. (2020). Optimized neural network model for attack detection in LTE network. Computers & Electrical Engineering, 88, 106879.
Li, J., Wen, M., & Zhang, T. (2015). Group-based authentication and key agreement with dynamic policy updating for MTC in LTE-A networks. IEEE Internet of Things Journal, 3(3), 408-417.
Li, J., Wen, M., & Zhang, T. (2015). Group-based authentication and key agreement with dynamic policy updating for MTC in LTE-A networks. IEEE Internet of Things Journal, 3(3), 408-417.